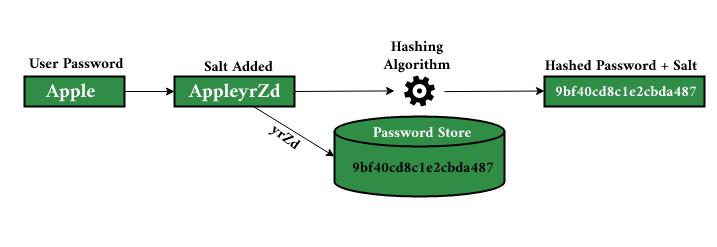
Salted password hashing can be used to improve password security by adding additional layers of randomness on top of the hashing process. Salt is a cryptographically secure random string that is added to a password before it’s hashed, and the salt should be stored with the hash, making it difficult for an attacker to know the original plaintext without having access to both sources. This process is often used in combination with bcrypt, another function that adds computing requirements for each and every attempt by an attacker who doesn’t have access to either source. Salted hashing is a much more complex and secure process because each hash requires the use of a different and random ‘salt’, that acts as an additional layer of encryption. This means that every known salt (or collection) is required to perform the password hashing function.
E-mail Attachments:
A sample E-mail containing an attachment is used to demonstrate how salted password hashes are applied in combination with bcrypt to create a secure, yet time-consuming, process for attackers. Bcrypt takes the input and produces a string of numbers that can then be converted into a password hash using various algorithms.
Attacking Unsalted Passwords:
Since the salt is not stored with the hash, attackers typically cannot determine which hashing scheme was used and therefore cannot reverse engineer the hash. Without an outside source of plaintext to compare a password hash with, attackers will be forced to guess brute force style. In order to brute force an unsalted password hash, you need both plaintext and password hashes. The hashes with the same plaintext must have the same salt so that there are only 2 choices, either you match both or you don’t match either. It’s much easier than guessing passwords one by one to find a matching hash pair, as it can be done in parallel.
Cracking Unsalted Hashes with Tables:
- Create a lookup table from O(1) to 2^(n/2)-1: A table of all the possible salt values can be found by simply generating random text strings and storing them.
- For example, in PHP you can do: echo md5(shuffling($salt))
- Generate all possible password hashes for your salt value and pipe it into your lookup table.
- Pick the number of hashes that match your original plaintext, and you will have the correct password for your salt value.
- To understand salted password hashing, you first need to understand how bcrypt works and what it does to generate a secure hash. Bcrypt is a function that takes an input string and produces one of many possible password hashes, depending on how much processing is required to generate each hash (similar to how MD5 has become outdated).
Mitigation and prevention:
- The value of the salt should be about as long as the maximum password length allowed by your application.
- The salt should be non-deterministic, a random string appended to each password before hashing is recommended.
- Salted passwords can be stored in a database rather than encrypted with a key since the hash will be different for each combination of salt and password, even though they use the same plaintext input string.
- To make it harder for attackers to reverse engineer the hashing, the salt should remain dynamic. Instead of using a single random string, you can use a random hash algorithm such as sha512 or bcrypt and store the pre-hashed password in a database.
- It is possible to have multiple salts for each user by using public/private keys for every account and salting each password separate from its corresponding public key (the private key is required to generate salted hashes).
- If the attacker has access to plaintext, they can still attack your salted hashes. This usually isn’t an issue because attackers typically have access to only one input source for all their attacks anyway.




