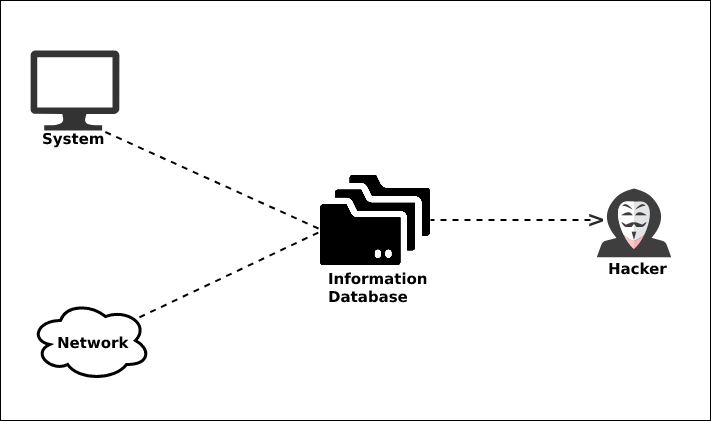
System hacking is the process of exploiting vulnerabilities in electronic systems for the purpose of gaining unauthorized access to those systems. Hackers use a variety of techniques and methods to access electronic systems, including phishing, social engineering, and password guessing.
Purpose of System Hacking:
Generally, the motive of the hackers behind System Hacking is gaining access to the personal data of an individual or sensitive information belonging to an organization in order to misuse the information and leak it which may cause a negative image of the organization in the minds of people, Privilege Escalation, Executing malicious applications to constantly monitor the system.
How this is carried out?
This type of hacking is generally done by a Hacker who has a lot of information regarding the System security, network, software, and how the system communicates with others in the network, often called Footprinting and Reconnaissance. Then these hackers try numerous ways to carry out the attack but the common ways are:
- By deploying Viruses, Worms, Malware, Trojans
- Using phishing techniques
- Social Engineering
- Identifying and exploiting Vulnerability
Steps:
1. Reconnaissance: The first step in this type of Hacking is collecting information regarding the System’s infrastructure, working, system’s network. This step is very important as after this step the Hacker knows what attack to perform and how to gain access without leaving a trace.
2. Scanning: This step involves scanning the target System, which includes:
- Vulnerability Scanning: Checking vulnerabilities in the targeted system that can be exploited to gain access.
- Mapping of Network: Finding the working of the network, firewalls, routers, and systems connected to it.
- Port Scanning: Scanning the open ports, and services running over the System/Server.
3. Gaining Access: This is the phase in which the hacker breaks into the system and gains unauthorized access to the System/Network and then elevates his privileges to that of Administrator or SuperUser so he can play with the System files that a normal/Guest user is unable to access.
4. Maintaining the Access: After the Hacker enters the System he tries to maintain the connection with it in the background until he accomplishes the goal with which he entered it.
To know more about the phases of hacking please refer to the article 5 Phases of Hacking.
Prevention from Hacking:
- Using Firewall.
- Installing Anti-Virus and Anti-Spyware packages.
- Keeping the system up-to-date as security patches updates comes regularly.
- Be Aware of various phishing techniques.
To know more about prevention please refer How to Protect Yourself From Cyber Attacks article.




