DNS Footprinting is a technique that is used by an attacker to gather DNS information about the target system. DNS Footprinting allows the attacker to obtain information about the DNS Zone Data, which includes:
- DNS Domain Names
- Computer Names
- IP Addresses
- Network related information
Some of the main records that are important in DNS Footprinting are as follows:
| Record | Description |
|---|---|
| A | A record is an address mapping record, also known as a DNS host record. |
| MX | The mail server record specifies an SMTP email server |
| NS | It specifies the authoritative Name Server. |
| CNAME | Conical Name record, alias record used to alias a hostname to another hostname |
| SOA | Start of Authority is the authoritative Name server for the current DNS zone. |
| PTR | Pointer records, It allows a DNS resolver to provide an IP address and receive a hostname |
| TXT | Text Record, It contains machine-readable data such as DKIM. |
| HINFO | Host information record includes CPU type and OS |
| SRV | Service Records |
Procedure:
DNS Footprinting is a simple procedure, we can perform DNS Footprinting by using various tools and websites but, here we are going to look at nslookup and dig.
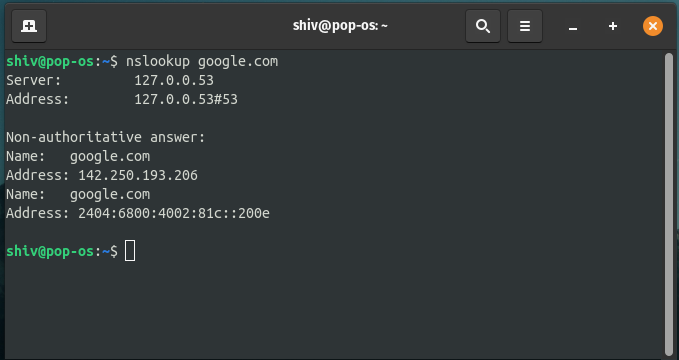
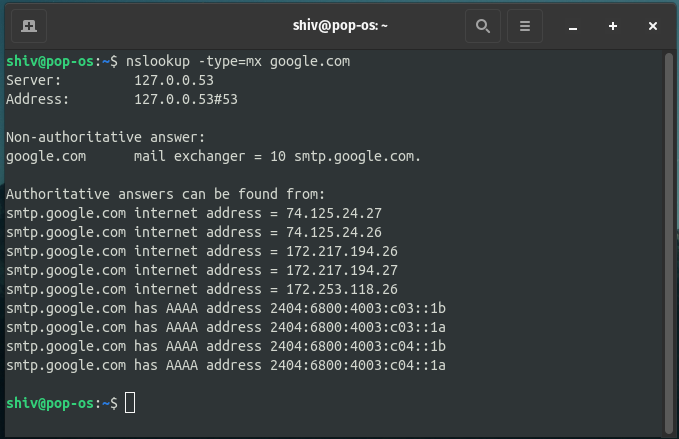
- NSLOOKUP: Nslookup is a network administration command-line tool for querying the Domain Name System (DNS) to obtain the mapping between a domain name and IP address or other DNS records. Nslookup’s usage commands:
nslookup <target domain> nslookup -type=<recordtype> <target domain>
Example:
- DIG: Dig is a network administration command-line tool for querying the Domain Name System (DNS). Dig’s usage command:
dig <target domain> dig <target domain> <record type> dig <target domain> any
Example:
Here in this example, we have used the second command from the above command list. We have used MX in place of record type to get information about MX records.
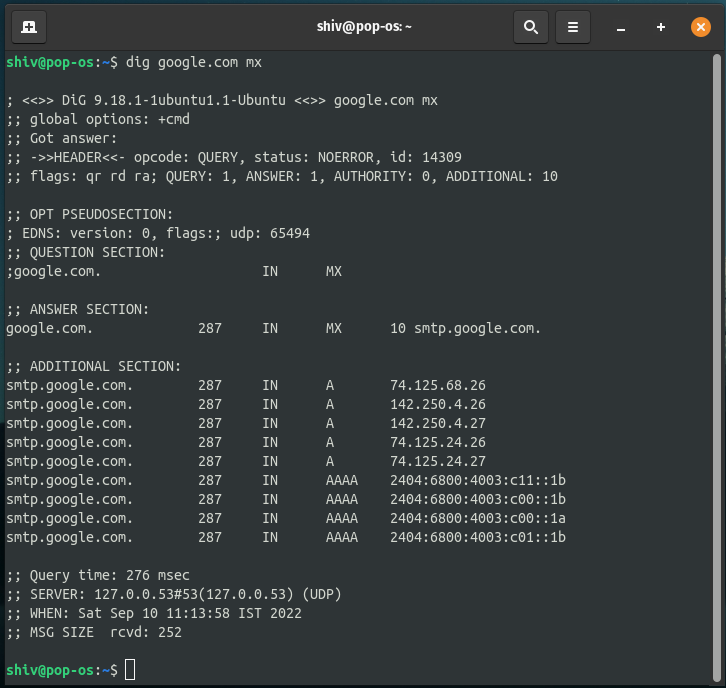
dig command usage
Output:
The above command provides the MX record as you can see in the terminal.
In this second example we have used the third command from the above command list i.e. ANY keyword, the ANY keyword just extracts all the possible records it can find on the server.
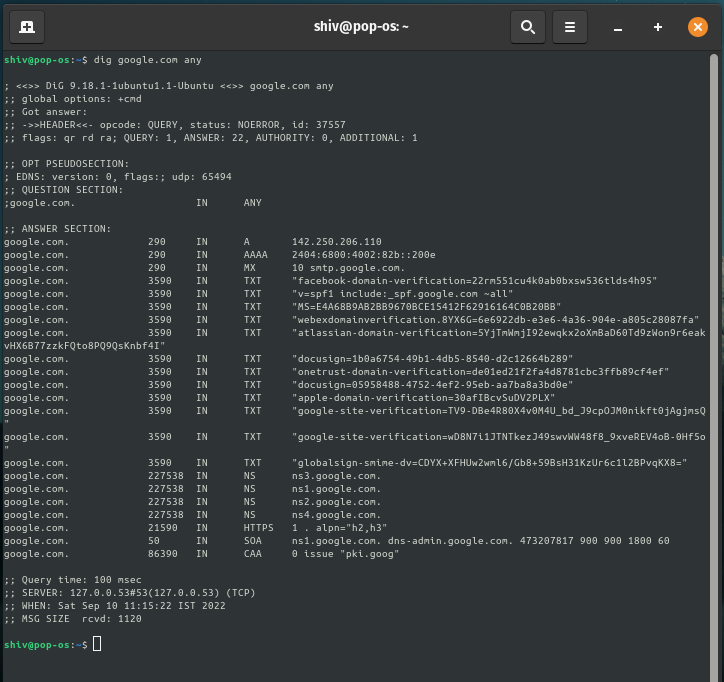
dig command usage
Output:
Using ANY keyword provides us with all the possible records as you can see in the result.




