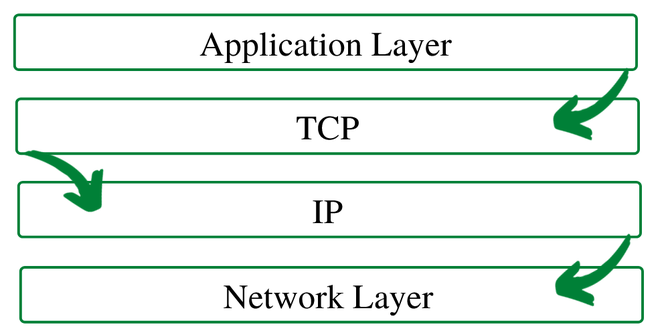
TCP/IP stands for Transmission Control Protocol/Internet Protocol. It is a communication protocol by which network devices interconnect on the internet and communicate with each other. The TCP protocol is used with an IP protocol, so both of them together are referred to as a TCP/IP. TCP/IP lies between the Application and Network Layers, which are used in providing reliable delivery service.
Working :
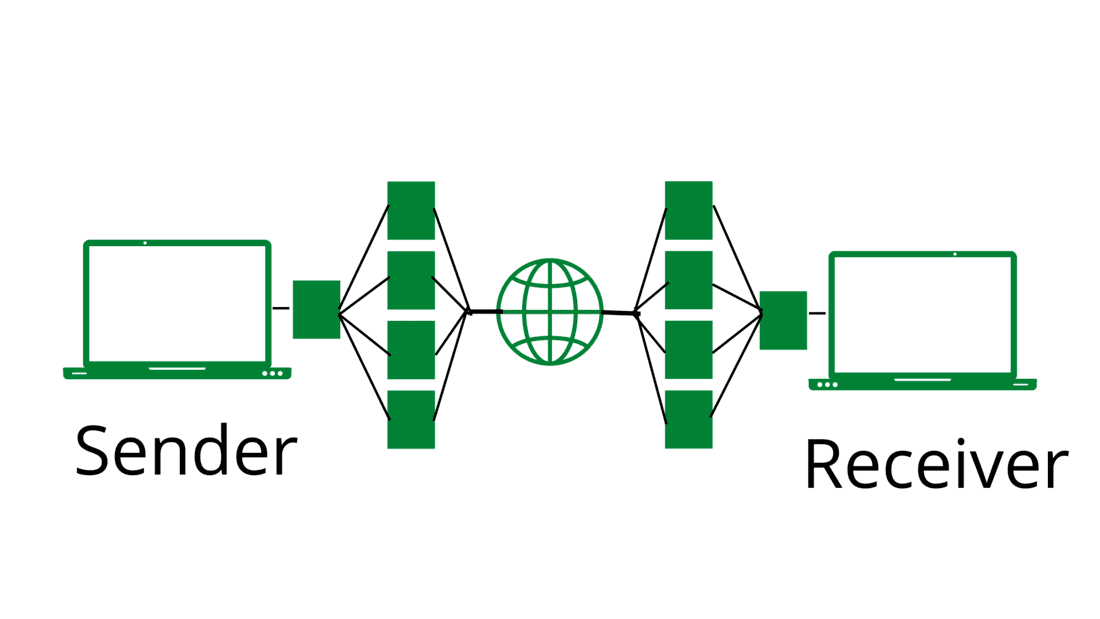
The TCP model breaks down sender messages or data into small packets and forwards them to the Internet Protocol (IP) layer. After the message is broken down into small packets, the packets are then sent through various routes to their destination. When one route is congested or cannot be used to reach the destination, then the packet arrives at the destination from multiple routes, but the destination remains the same during the process. When the packets arrive at their destination, they are reassembled into the original message or data, and the receiver receives the message or data. The TCP layer in the sender system waits for the end of the transfer and acknowledges when all packets are received.
TCP/IP Hijacking:
TCP/IP hijacking is a man-in-the-middle network attack. This is a network attack where an authorized user can gain access to another user’s or client’s authorized network connection. After hijacking a TCP/IP session, an attacker is able to easily read and modify the transferred packets and the hacker is also able to send its own requests to the user. For TCP/IP hijacking, attackers use DOS attacks and IP spoofing.
TCP/IP Hijacking Process:
- The first major goal of an attacker is to obtain the IPs of two devices that communicate using the same network or connection. To do this, the attacker monitors the data transmission on the network until the IP of the device is obtained.
- After successfully grabbing the user IP. Hackers can easily attack the connection.
- In order to gain access to the connection, the hacker put down the connection of another user through a DOS attack, and the user’s connection waits for reconnection.
- By spoofing the disconnected user’s IP, hackers can easily restore communication.
Preventive Measures:
- Do not click on unwanted or unknown links.
- Check the web application for all errors.
- Use an Intrusion Detection System (IDS) to monitor network traffic for unwanted or unknown activity and detect ARP spoofing/poisoning.
- Use a switch instead of a hub for increased security.
- Always send the session ID over SSL for increasing security.
- Use a different number of session IDs for each page.
- Always use a secure protocol like HTTP instead of a plain text protocol like HTTP, until you don’t know which is right.