15 System Design Building Blocks You Should Know
System design can feel complex, but once you understand its fundamental building blocks and how to stitch them together, everything falls into place.
In this post, we’re going to break down the top 15 building blocks of system design, every developer should know.
Knowing these will help you make sense of a large system and help you in answering your next system design interview problem.
📣 Design, develop and manage distributed software better (Sponsored)
Multiplayer auto-documents your system, from the high-level logical architecture down to the individual components, APIs, dependencies, and environments. Perfect for teams who want to speed up their workflows and consolidate their technical assets.
1. Load Balancers
Load balancers distribute incoming requests across multiple servers to ensure no single server bears too much load. It helps maintain availability and reliability by automatically rerouting traffic if a server fails.
Use it when your application grows beyond the capacity of a single server and needs horizontal scaling to maintain performance and availability.
Types:
-
Layer 4 Load Balancers: Operate at the transport layer (e.g., TCP, UDP).
-
Layer 7 Load Balancers: Operate at the application layer (e.g., HTTP, HTTPS).
Examples: Nginx, HAProxy, AWS ELB
2. Reverse Proxy
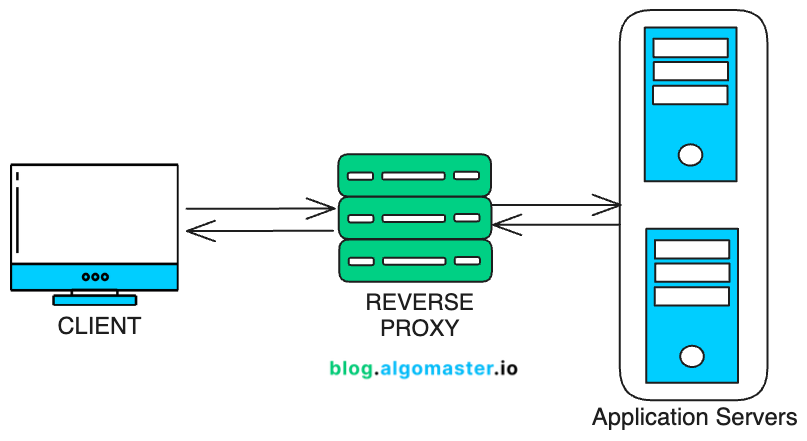
A reverse proxy acts as an intermediary between clients and servers. It forwards client requests to appropriate backend servers and then returns the server’s response back to the client.
It enhances security by hiding the backend servers and optimizes performance through caching.
Example: Cloudflare acts as a reverse proxy for websites, securing and accelerating content delivery by caching resources and blocking malicious traffic.


